Products
Full Width
{{/if}} {{/if}}-
{{#each price-tray.productOffers}}
{{leftCurrency}}{{price}}{{#if cents}}{{decimalSeparator}}{{/if}}{{cents}}{{rightCurrency}} Buy {{#if hasStore}} {{/if}}{{else}}{{/each}}{{#each price-tray.promotions}} {{/each}}
{{name}}
{{name}}
{{address}}
{{city}}, {{state}} {{postCode}}
{{phone}}
{{/if}}Advanced Search
Using Intel.com Search
You can easily search the entire Intel.com site in several ways.
- Brand Name: Core i9
- Document Number: 123456
- Code Name: Kaby Lake
- Special Operators: “Ice Lake”, Ice AND Lake, Ice OR Lake, Ice*
Quick Links
Try these quick links to visit popular site sections
Recent Searches
Automatically update your drivers and software
Use this tool to identify your products and get driver and software updates for your Intel hardware.

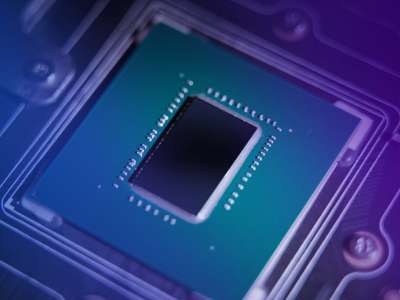
Intel® Processors for All That You Do
Intel sets the industry standard for processor innovation and performance, powering laptops, desktops, workstations and servers—for business and personal use, immersive gaming, content creation, IoT, Artificial Intelligence, and more.

Intel® Xeon® Scalable Processors
3rd Generation Intel® Xeon® Scalable processors offer a balanced architecture that delivers built-in AI acceleration and advanced security capabilities. This allows you to place your workloads where they perform best - from edge to cloud.

Intel® Xeon® Processors
Optimized performance, scale, and efficiency across a broad range of data center, edge, and workstation workloads. Elevate business productivity with the consistent, open, Intel® architecture you know and trust.

Intel® Core™ Processor Family
Do it all and be it all with more performance and efficiency. Welcome to a new level of creating, gaming, and connecting.

Intel® Pentium® Processors
Discover an amazing balance of performance, experience, and value with systems powered by Intel® Pentium® processors. These processors power more devices, from notebooks to convertibles to desktops and mini PCs—Supports Windows, Chrome and Linux OS—giving you flexibility to choose the best device for your needs, while knowing it will give you the performance, experiences, and security features you deserve.

Intel® Celeron® Processors
Intel’s Entry level PCs can help users collaborate, create, learn and play like never before. Users can enjoy the great experiences they have wanted from their Notebook, Chromebook, Convertible, or Desktop PC, with the security and connectivity options for a protected modern lifestyle.

Intel Atom® Processor Family
Deliver advanced technology and processing capabilities where you need it most with cost effective, durable, and flexible Intel Atom® processors for network infrastructure, network security, and storage appliances.

IoT and Embedded Processors
Deploy edge applications quickly with Intel's portfolio of edge-ready compute and connectivity technologies. Enhanced for IoT, they enable processing at the edge to get critical insights and business value from your data with compute resources where you need them most.

Intel® Server Products
Driving Data Center Transformation through innovation, trust, reliability, and proven performance. There are reasons Intel is a global leader and preferred provider of server technology and products. Intel understands the needs of the modern data center and harnesses its years of experience and design expertise to deliver a broad portfolio of innovative server products, systems, and solutions to help businesses grow and be competitive in the market.

Intel ASICs Products
High quality ASICs products to fit your needs.

Intel® Graphics Solutions
Intel’s GPU technologies deliver true-to-life graphics with superior performance, speed, efficiency, and scalability.
Memory and Storage
Intel provides technically advanced products that support every level of computing—from data center workloads to enthusiast usage. Intel® Optane™ memory creates an accelerated bridge between memory and storage. Intel® Solid State Drives (Intel® SSDs) provide storage flexibility, stability, and efficiency.
Intel® Wireless Products
Get fast, integrated wireless solutions which deliver great user experiences and meet our growing demands for higher bandwidth, improved responsiveness, and enhanced reliability.

Edge-to-Cloud Network Connectivity
Intel delivers a full portfolio of high performance, flexible networking products that meet the demands of cloud, telecom, enterprise, storage and more. Explore our products here.

FPGAs & Programmable Devices
Get the flexibility you need and accelerate your innovation with a broad portfolio of programmable logic products including FPGAs, CPLDs, Structured ASICs, acceleration platforms, software, and IP.

Windows® 10 and Windows 11* Wi-Fi Drivers
Version 22.200.2.1 installs the Windows®10 64-bit and Windows 11* Wi-Fi drivers for the following Intel® Wireless Adapters: AX411, AX211, AX210, AX203, AX201, AX200, AX101, 9560, 9462, 9461, 9260

System Manufacturers Support
Find drivers, software, and support information from these original equipment manufacturers.
No results found for "${query}"
No results found for "${query}"
Search tips:
- Remove any search filters to broaden results
- Sign in or register to include any results that may be restricted
- Make sure all words are spelled correctly
- Use different or more general keywords
Date Range
No results found for "${query}"
No results found for "${query}"
Search tips:
- Remove any search filters to broaden results
- Sign in or register to include any results that may be restricted
- Make sure all words are spelled correctly
- Use different or more general keywords
This website contains Intel's confidential information, which may only be used and disclosed in accordance with the applicable non-disclosure agreement between you or your company and Intel.
Product and Performance Information
Retail prices reported as of